

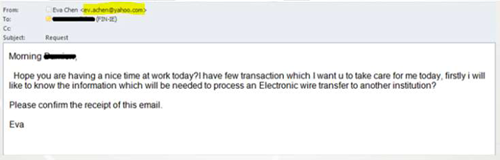
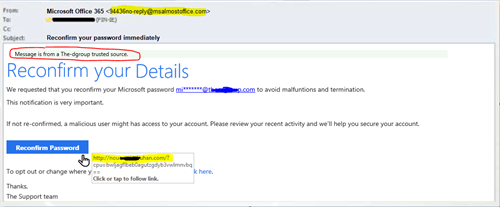
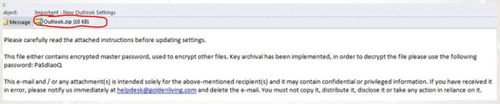
Phishing is a social engineering tactic where a malicious actor uses online communication (Email, txt, or instant messaging) to deceive you into giving out sensitive information, banking information or your passwords to access it. Typically, the messages pretend to come from well-known and trustworthy web sites or high-ranking authority figures.
You can read more on how to recognize email scams at https://www.us-cert.gov/sites/default/files/publications/emailscams_0905.pdf.
This material is provided by The Scylla Group, Inc. for use by our clients and customers of Trend Micro Antivirus and Security products. Some content was supplied from Trend Micro provided Phishing Awareness Training via a corporate partnership.