

Two-Factor Authentication is sometimes called Multi-Factor Authentication, Two-Step Verification, or 2FA. But, no matter what you call it, it is an effective tool for fighting PHISHING, data loss and other malicious attacks.
Two factor authentication requires that a user present something they "have" in addition to something they "know" when signing on.
THE FIRST FACTOR:
The "something you know", is the way you've been logging in for years. It is typically just typing in your username and password. You hopefully have your password(s) memorized, not shared with others, and not written on a sticky note under your keybaord. But, with the rise of phishing attacks, data leaks, and general carelessness, just providing a username and password isn't enough to keep your services secure anymore.
THE SECOND FACTOR:
The “something you have” portion for authentication can bet many different things, but the most common one you’ve probably seen is getting a PIN code via txt message whenever you sign into your credit card’s website. Using txt messages as a 2nd factor is OK, but there are better and more secure options available too. Here are a few of the most common two-factor implementations:
Each of these implementations has its strengths and weaknesses, so it is a good idea to speak with an IT professional about your requirements, but pin codes via txt and email are generally considered the weakest options. It has become really common for scammers to clone or even transfer ownership of phone numbers to get what they want (especially when bitcoin is involved). Using your email address may work for some services, but it doesn't work for access to your email account and isn't very good if your email isn't protected by two-factor itself. Physical devices are some of the strongest options, but software tokens on a mobile device could be a good compromise for your environment and needs.
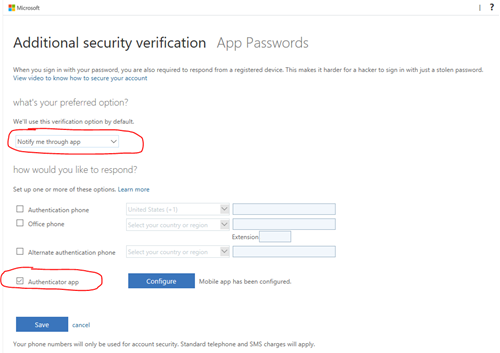
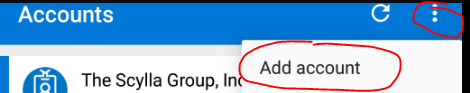
Microsoft Office 365 allows you to use many industry compliant OAUTH mobile device applications for your second factor, but it integrates best with their own client called Microsoft Authenticator. It can be installed on your iOS, Android or Windows device. Once enabled, you simply log into Office 365 with your username and password and the Microsoft Authenticator app on your mobile phone will prompt you to allow the logon. If you didn’t try to logon, then you know that someone is trying to access your account and you can deny it. If you did try to logon, you simply tap approve and the site will continue with the logon process.
HOW DO I ENABLE 2FA?
We recommend enabling two-factor authentication for all of your logons and services that support it. Most common services like Gmail, Facebook, LinkedIN, Twitter, and more support it. But, we are going to focus on how to enable it in Microsoft Office 365 since we are a Microsoft partner and this is where we use it most often.
You can read more how Microsoft has implemented multi-factor authentication in Office 365 and Azure by going to https://docs.microsoft.com/en-us/azure/active-directory/authentication/concept-mfa-howitworks.